You no longer have to use TOTP tokens on Linux; now, you can get the same user experience as on other operating systems—it's time to improve MFA authentication using the Golang tool Linux-id to get closer to MFA capabilities on different operating systems.
In this post, I'll explain how the Linux-id tool works to enhance second-factor authentication on Linux.
The process involves installation, registration of a new token, and authentication.
Table of Contents
This post includes the following sections:
- MFA - Multi-Factor Authentication in more detail
- Showcase - This section showcases the
Linux-IDtool. - Setup - How to setup
Linux-ID. - How it works - Explanation of the Linux-ID functioning.
- Fork - The original project
- Repository - Link to
Linux-ID.
MFA
MFA, or Multi-Factor Authentication, is typically done in several ways: via SMS, email, OTP, TOTP, and FIDO keys such as Yubikey or a key stored in a TPM (Trusted Platform Module). The last way, which is the easiest for the user, is used by Windows Hello and Apple ID; thanks to this tool, you can achieve similar functionality.
Showcase
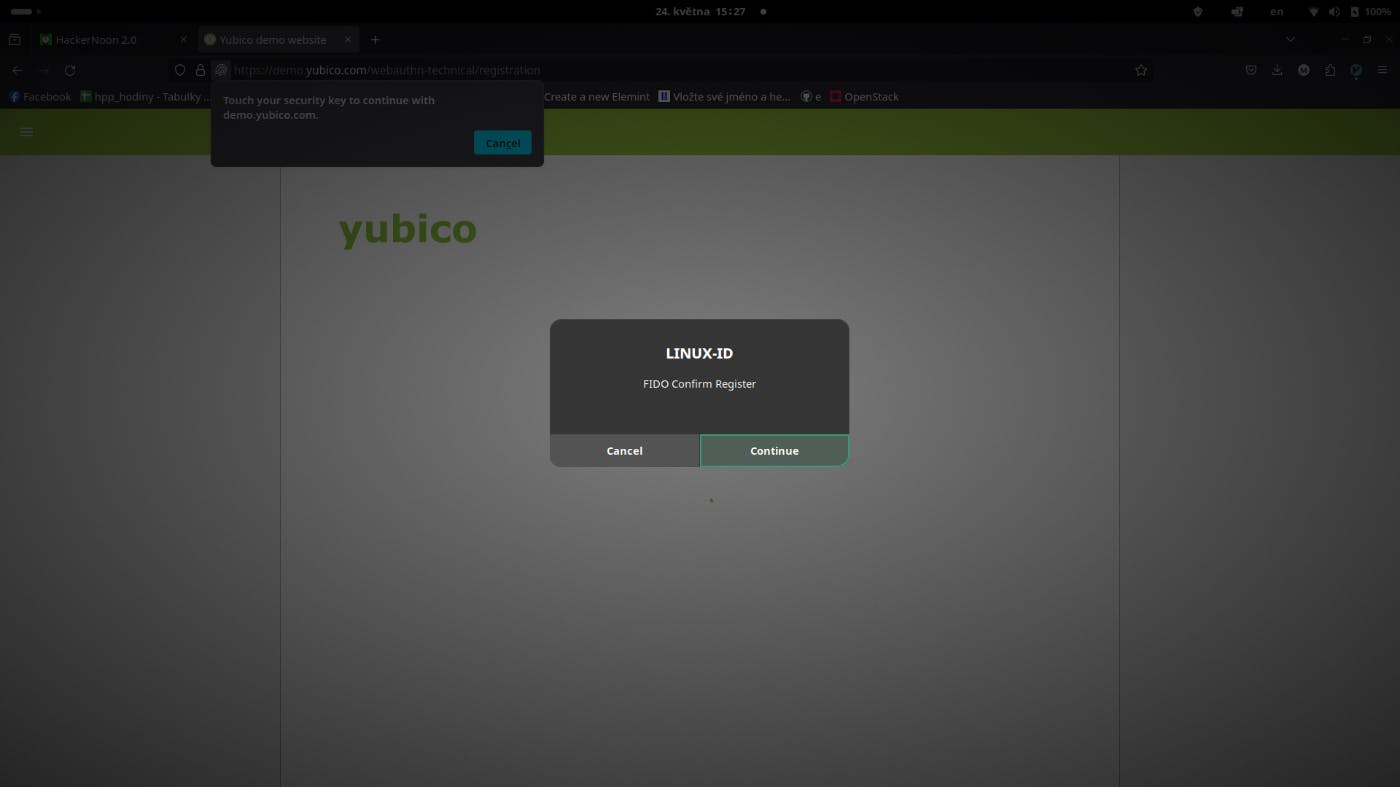
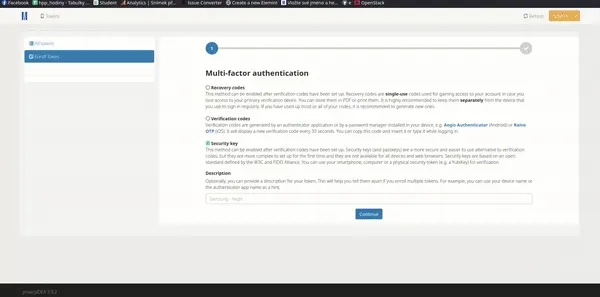
In the GIF below, you can see the whole workflow.
- First, I registered the
Linux-idin the Unified Login to use it for Web Authentification. - Then, I click on a new tab where I am not logged in and perform the sign-up process with the Linux-id tool as MFA.
Setup
You can install it by running the following commands:
git clone git@github.com:matejsmycka/linux-id.git cd linux-id
go install
chmod +x install.sh ./install.sh
Or you can download the latest release without installing Go:
curl -L https://github.com/matejsmycka/linux-id/releases/download/v0.1.1/linux-id_Linux_x86_64.tar.gz | tar xz chmod +x linux-id curl https://raw.githubusercontent.com/matejsmycka/linux-id/main/install.sh | bash
How It Works
-
On registration, linux-id generates a new P256 primary key under the Owner hierarchy on the TPM. To ensure that the key is unique per site and registration, linux-id generates a random 20-byte seed for each registration.
-
The primary key template is populated with unique values from a sha256 HKDF of the 20-byte random seed and the application parameter provided by the browser.
-
A signing child key is then generated from that primary key. The key handle returned to the caller concatenates the child key's public and private key handles and the 20-byte seed.
-
On an authentication request, linux-id will attempt to load the primary key by initializing the hkdf in the same manner as above. It will then attempt to load the child key from the provided key handle. Any incorrect values or values created by a different TPM will fail to load.
Fork
This project is a fork of Psanford's tpm-fido project. To be transparent, this would not have been possible without his contributions, and I am grateful to him for creating this unique project.
However, after a discussion with the author, I created a new repository because I had different ideas about the project.
The key differences are:
- This project aims to be more accessible to average users.
- I have updated old methods according to the latest Go standards.
- Old dependencies (e.g. pinetry) were replaced with updated ones.
- UX improvements.
Repository
Visit the Linux-ID for more information.